Is Reusing Passwords Worth the Risk?
You’ve probably heard the advice about not reusing passwords. Maybe it’s even advice that you put into practice most of the time. Until you’re signing up for an online streaming service and as you briefly consider entering a unique, 20-digit randomly-generated password, the idea fills you with dread. Not only do you have to enter that password across multiple devices, but the rest of your family will too.
Maybe you could turn it into a game: pass around the hand-written sticky-note and guess is that’s a “1” or an “l”…you decide to reuse a password that everyone already knows instead. It just happens to be the same password as your two other existing streaming accounts. But at that moment, the hassle you just avoided is definitely worth the risk.
So how risky is reusing passwords? It depends on how often you reuse passwords, where you reuse them, and luck. But here’s a recent example that gives even the occasional password re-user a little pause.
A new streaming service launched in November, and within hours, customers were having trouble accessing their accounts. Hackers logged subscribers out of their accounts and changed their email addresses and passwords, leaving them unable to get back in. Understandably upset by getting locked out of their brand new accounts, users took their frustrations out on the streaming service. What had happened? Was the service hacked?
What subscribers couldn’t have known was that almost as soon as the streaming service launched, hacking forums began featuring lists of the user and password combinations for thousands of valid streaming accounts. Some accounts were for sale, and others offered as free to use.
Since there was no evidence of a data breach, the most likely explanation is that hackers were using a technique called credential stuffing. This technique begins with an older list of stolen username and password pairs, or credentials, from a previous hack. The list of user and password combinations are then “stuffed” into an entirely different website, in this case, a new streaming service, to see if any of them worked.
Hacking tools created for this purpose are readily available, not only for automating this process but for masking the typical signs of this activity as it’s happening within the network, making it considerably harder to stop. Within hours, hackers were able to assemble lists of active accounts and post them on hacking forums to trade or sell.
Some hackers may want “free” streaming content, but that would be the most benign reason to use a stolen account. Many hackers purchase lists of active account credentials to use as a starting point for more advanced types of cybercrimes. Beginning with access to one, hackers can use a variety of additional hacking techniques such as phishing or malware to start taking over email or financial accounts.
The basis for credential stuffing as a technique, and one of the main reasons that these credential lists even have value within the hacking community, is the enduring human tendency to reuse passwords. Last January, a security researcher discovered the first of five extraordinarily large lists of credentials. These lists were from many previous data breaches and combined into five massive collections.
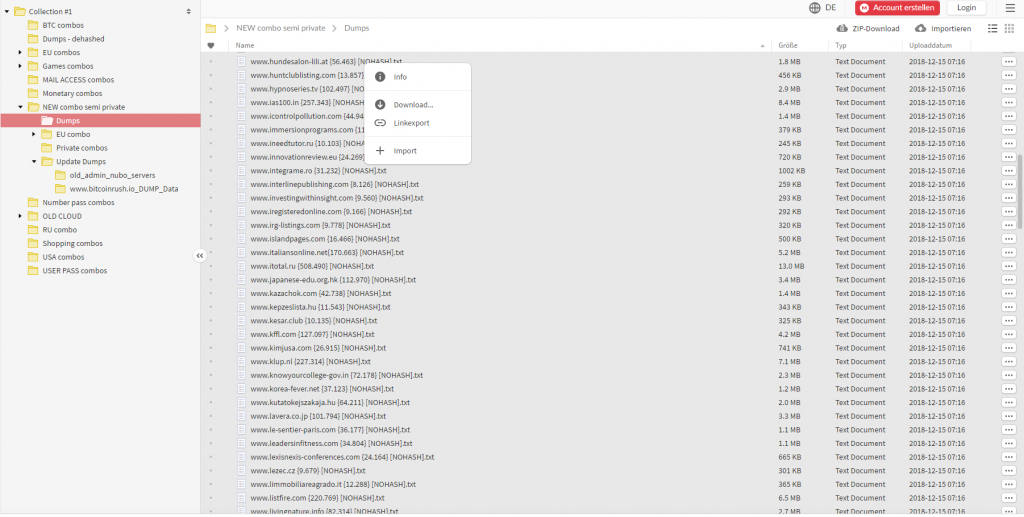
Source: troyhunt.com
Known as “Collection #1-5”, they contain a staggering total of 2.2 billion credential sets. Stolen credential lists have always been a tool for hackers, but security experts were unprepared for the scale of this collection. Using credential stuffing on a popular new streaming service is noteworthy. Still, it’s just one of many recent examples of a security issue that shows no signs of slowing down.
Websites often include instructions about how to create a unique and complex password during the creation of a new online account. However, these kinds of directions haven’t done a whole lot for establishing safer password habits in reality. Passwords need to be easy to remember, and that typically decreases their complexity. And with so many online accounts and applications, remembering a different password for each one is impossible. Many websites now offer two-factor authentication as a stop-gap approach to protect their customers (and themselves) from some of the security issues with passwords. Two-factor authentication isn’t a perfect solution, since having an opt-in approach always leaves out the users that don’t want the hassle of an additional security step.
Using a good password manager is the best way to overcome the majority of these password-related issues and improve the security of your data overall. A password manager will automatically generate and remember the password for each account. They can be used on multiple devices and shared by a family or even a business. A few downsides to a password manager are the setup process and the typical learning curve that comes with any new application. They also typically require a monthly or annual fee to use.
While not perfect, password managers provide a workable solution, making it convenient to use password best practices, improving the security of your online accounts across-the-board. If you’ve been a chronic password re-user, it will be a great tool to help you get all those old passwords changed. With a collection of 2.2 billion credential pairs floating around out there, a password manager is unquestionably worth it.
References:
Barrett, Brian. 2019, November 20. The Likely Reason Disney+ Accounts Are Getting ‘Hacked’. Retrieved from https://www.wired.com/story/disney-plus-hacks-credential-stuffing/
Greenberg, Andy. 2019, January 30. Hackers Are Passing Around a Megaleak of 2.2 Billion Records. Retrieved from https://www.wired.com/story/collection-leak-usernames-passwords-billions/
Cimpanu, Catalin. 2019, November 16. Thousands of hacked Disney+ accounts are already for sale on hacking forums. Retrieved from https://www.zdnet.com/article/thousands-of-hacked-disney-accounts-are-already-for-sale-on-hacking-forums/
